We were recently informed of a not-for-profit that was the victim of cybercrime when their website hosting provider was hacked. They only discovered the breach when they began to receive calls from their members questioning why the organisation was enquiring about their financial information. These phone calls marked the start of the most stressful two weeks the organisation had ever encountered. The security incident resulted in their not-for-profit blacking out for over 72 hours in the middle of a major fundraising event. They were also faced with an investigation from the Australian federal government which led to paying hefty penalties in addition to receiving backlash from their donors.
This story is an important reminder that not-for-profits (or any organisation for that matter) that collect data are responsible for keeping it safe. Unfortunately, we see that most not-for-profits are unable to do so adequately because of the following key reasons:
- Lack of IT security knowledge or personnel.
- No integrated security tools and solutions.
- Reliance on traditional, perimeter-based security tools.
- Use of outdated hardware and software.
- Limited financial resources.
- Lack of measurable IT security strategy.
Cybercriminals have become more persistent, the threats are harder to detect, and every year many not-for-profits experience a cyber security incident in one form or another. In fact, the 2022 Annual Cyber Threat Report by the Australian Cyber Security Centre (ACSC) reported over 76,000 cybercrime incidents, an increase of nearly 13% from the previous financial year. That’s equivalent to 8 cyber incidents an hour.
To ensure your not-for-profit doesn’t become another part of the cybercrime statistics, you must protect your beneficiaries’ and donors’ data by implementing proven security controls and tools. An excellent way to get started is to align with a measurable and industry-recommended cyber security strategy such as Essential Eight and use the security tools in Microsoft 365 to put it into practice.
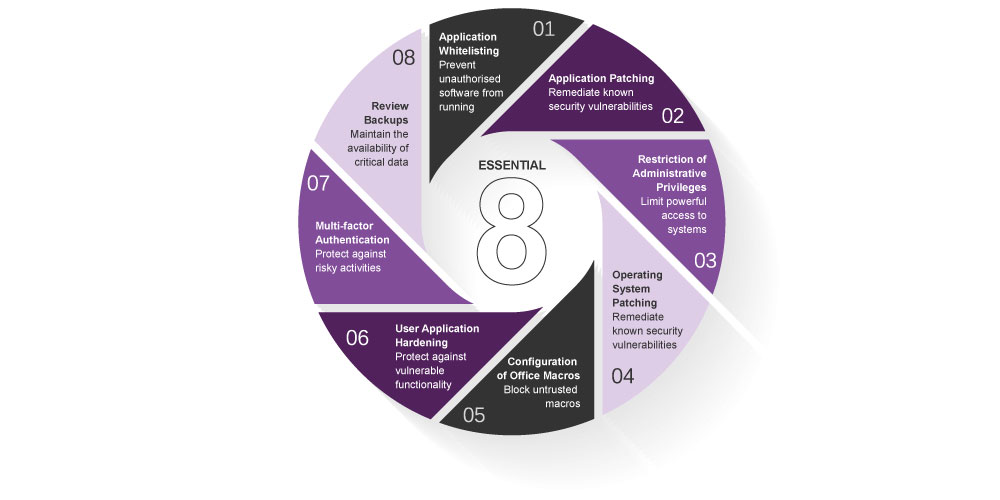
Developed by the Australian Signals Directorate (ASD), Essential Eight is a prioritised list of risk mitigation strategies designed to help organisations protect against cybersecurity threats and reduce the risk of a successful cyber attack. Each security control helps your not-for-profit mitigate your cyber risks in these ways:
- Application Whitelisting: prevent unauthorised software from running.
- Application Patching: remediate known security vulnerabilities.
- Restriction of Administrative Privileges: limit powerful access to systems.
- Operating System Hardening: remediate known security vulnerabilities.
- Configuration of Office Macros: block untrusted macros.
- User Application Hardening: protect against vulnerable functionality.
- Multi-factor Authentication: protect against risk activities.
- Review Backups: maintain the availability of critical data.
Professional Advantage and Microsoft 365 can help your not-for-profit put Essential Eight into practice to improve your security posture while saving on licensing costs. These Microsoft 365 tools (along with Microsoft Azure) can help you comply with Essential Eight:
- Application Whitelisting: AppLocker, Windows Defender Suite, and Application Control.
- Application Patching: Microsoft Intune and Winget.
- Restriction of Administrative Privileges: Microsoft 365 role-based access control.
- Operating System Hardening: Automatic updates.
- Configuration of Office Macros: Manage Macros, Intune Attack Surface Management.
- User Application Hardening: Intune Attack Surface Management.
- Multi-factor Authentication: Microsoft 365 MFA.
- Review Backups: Azure Backup and Azure Site Recovery.
Microsoft Solutions for Essential Eight Compliance
Learn how Professional Advantage, Essential Eight, and Microsoft 365 can help improve your not-for-profit’s cybersecurity posture. Read the complete executive guide: “Protect your not-for-profit with Essential Eight and Microsoft 365”.
Alternatively, you can watch our on-demand webinar, Essential Eight Cybersecurity from the Server Room to the Boardroom.





